What is Cloud Security?
In recent years, companies have redesigned their IT infrastructure in order to remain competitive. They have thus made the balance between keeping their IT resources on-premise or migrating to Cloud Providers.
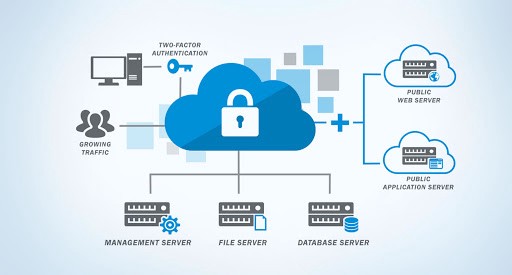
Cloud security is a discipline that originated from cybersecurity. It is dedicated to securing IT systems in the Cloud. Its purpose is to maintain the privacy and security of data and applications. You will also often hear about DevSecOps, which is the collaboration between developers, ops, and security teams. This is essential to establish a sound security strategy in your company.
Generally speaking, security in the cloud makes it possible, among other things, to protect the elements below:
- Data server
- The information stored
- Applications
On-premise security vs cloud security?
One of the first questions that emerge concerns the difference in security between Cloud and on-premise.
When we speak of on-premise, we imply that the servers and data are located within the companies. Companies then have an internal IT department that takes care of the management and maintenance of the network.
If data security may seem optimal, because it is managed by the company, it turns out that most on-premise systems are not equipped to ensure a high level of security on different system layers (infra, network, application, data). Furthermore, it should be noted that the basic investments are substantial and that the scalability of the infrastructure remains complex and includes additional costs.
Managing your security on an on-premise infrastructure certainly allows you to have a high level of customization, but in return requires having within your teams, people who are experts in the field of security.
Cloud security resides on a model of shared responsibility, which we will discuss below. Today, Cloud Providers offer a secure base system, regularly updated to mitigate potential attacks.
Public cloud-based services involve trusting a third party with your most valuable data, but on the other hand, they are experts to lean on.
Finally, it is important to ensure that your cloud provider allows compliance with the necessary regulations on compliance aspects.
What is the company’s responsibility for cloud security?
The sole responsibility for Cloud security does not rest exclusively with the Provider, as data and applications are moved there.
Migration to the cloud requires the company to take action to protect servers, storage, applications, and data.
Cloud service providers will offer fairly robust security controls depending on the service offer chosen. But the company remains dependent on protecting its assets.
If we take the example of AWS as a Provider:
- AWS will be responsible for the security of the Cloud and therefore for the protection of the infrastructures that use the services offered by AWS.
- The customer’s responsibility will be determined according to the AWS Cloud services chosen. Services determine the level of configuration the customer will need to perform as part of their security responsibility.
What cloud security threats to prepare for?
A second question arises: the nature of the security threats to be prepared for when migrating to the cloud?
If the Cloud is considered secure, companies today are under increasing threat from malware, virus attacks, or breaches at the network level. Of course, the threats depend in part on the existing architecture, database, applications, and the nature of the business itself.
The main security threats are:
- Insecure interfaces and APIs
- Misconfiguration of the platform
- Data Breaches, Losses, and Leaks
- Hijacking of accounts
- Internal threats
In summary, the security threats remain quite similar on on-premises or in the Cloud. The providers are responsible for the security of their services and are also able to detect attacks that do not depend on their scope but on that of the company. Finally, one of the most damaging things is the lack of skills of IT teams in Cloud technologies which can weaken the security of infrastructures.
Are there strategies or tools to have a secure Cloud?
There are different strategies that can be put in place to guarantee the security of your Cloud:
- Have a well-implemented Identity and Access Management (IAM) system to control access to data and define rights. Strong or two-factor authentication is a widely recommended practice
- Install detection and prevention systems:
- IDS: Intrusion detection and network monitoring system that detects malicious activity. The objective of this system is to preserve the security of the systems in the event of technological failure.
- IPS: Intrusion prevention system whose objective is to control access to the computer network. This type of system will monitor intrusion data and implement corrective actions.
- Perform vulnerability scans and penetration tests on Cloud security infrastructure to identify potential flaws.
To conclude, security in the Cloud security will allow you to achieve one or more objectives:
- Quickly recover your data in case of loss if you have made good backups beforehand
- Reduce human error
- Reduce the risk of data/system compromise if your Cloud Provider attacks are detected